Definition • May 28, 2025
What is patch management in IT? Definition, best practices and tools
Why is patch management crucial to IT security? Definition, processes, risks and recommended software.

Tip Incident management process, to transform crises into opportunities for continuous improvement Discover why and how to set up a standardized incident management procedure, and a selection of software to support you.

Tip Why is it (absolutely) necessary to adopt an IT security policy in your company? Viruses, cyber-attacks, hacking, espionage, data loss and more. In the face of these threats, make sure you adopt an IT security policy.

Definition What is a botnet? Everything you need to know to protect your devices from attack A botnet can turn your device into a weapon without you even knowing it. Find out how they work, what they're used for and how to protect yourself effectively.

Definition • May 28, 2025
What is patch management in IT? Definition, best practices and tools
Why is patch management crucial to IT security? Definition, processes, risks and recommended software.

Definition • May 28, 2025
10 different types of computer attack to be aware of in 2025
Learn to identify the 10 most common types of computer attack in 2025 and discover how to better protect your data in the face of new threats.

Software • May 16, 2025
Protect your data with anti-ransomware software: our top 10
Discover our list of the best anti-ransomware software of 2025. Key features, price, benefits, we compare all the offerings.

Definition • April 30, 2025
Deciphering the phishing attack, so you don't take the bait!
Find out what a phishing attack is, how to recognize it and what measures to take to protect your personal and business data effectively.

Definition • April 30, 2025
Whaling, or when hackers target the big fish
Find out what whaling is, a targeted form of phishing aimed at executives, and learn how to detect it with practical tips and tailored cybersecurity tools.

Definition • April 29, 2025
The computer worm, a threat that crawls... and strikes fast!
We've put together a complete guide, including security measures, to help you learn everything you need to know about the computer worm, the threat that crawls and strikes fast!

Kaspersky Small Office Security ufvhb ju
Cybersecurity
Antivirus
Computer Security
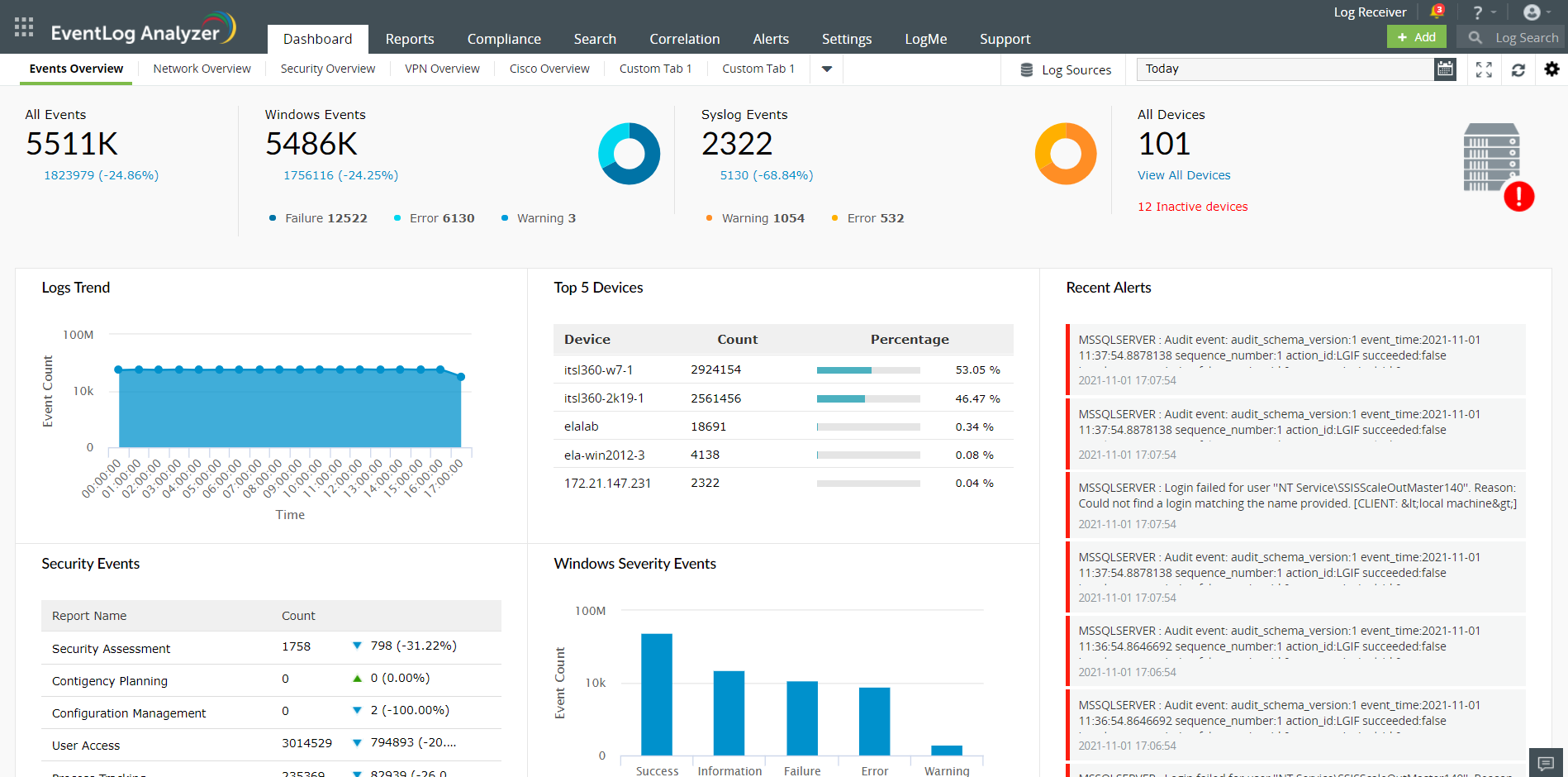
ManageEngine EventLog Analyzer
Log Management
Learn more about ManageEngine EventLog Analyzer

Mailinblack
Cybersecurity
Learn more about Mailinblack

ManageEngine Endpoint Central
IT Monitoring
Learn more about ManageEngine Endpoint Central
Merox
Computer Security
Learn more about Merox
iLock Security Services
Computer Security
Learn more about iLock Security Services
XyLoc Security Server
Computer Security
Learn more about XyLoc Security Server
inWebo
Computer Security
Learn more about inWebo
Splunk Enterprise Security
Computer Security
Learn more about Splunk Enterprise Security
DatAlert
Computer Security
Learn more about DatAlert
Data Classification
Computer Security
Learn more about Data Classification
Stormshield Endpoint security
Computer Security
Learn more about Stormshield Endpoint security
E MAIL SECURITY
Computer Security
Learn more about E MAIL SECURITY

Tip • April 28, 2025
Between best practices and tools, how to guarantee your company's IT security
What are the main IT security risks facing your company? This article guides you through the best practices for ensuring your protection, and the essential tools to help you do it.

Definition • April 25, 2025
The magic link, or how to combine user experience and cybersecurity
Discover what a magic link is: a password-free authentication method that's simple, fast and secure. Benefits, how it works, use cases... we explain it all!

Tip • November 13, 2024
How can you protect your business from cryptoviruses?
Cryptoviruses are malicious software programs. Increasingly frequent, they require upstream intervention to limit the damage.

Tip • October 29, 2024
Cybercrime: examples and measures to protect sensitive projects
Lionel Roux, CEO of Wimi, makes us aware of the dangers lurking in IT security, and gives us some excellent advice on how to guard against threats.

Definition • October 29, 2024
Shadow IT: a new threat to corporate IT security?
What is shadow IT, a practice increasingly encountered in the enterprise? We take a look at the risks, opportunities and ways forward for shadow IT.

Definition • October 29, 2024
How can DMARC authenticate your e-mails?
5 letters for 2 main issues: less spam and more deliverability for your e-mails. Authenticate your e-mails, improve your reputation and stand out from the crowd!

Definition • October 29, 2024
Dictionary attack: what if a password dictionary was the solution?
A password dictionary isn't just useful for hackers. Companies can also use them to check the strength of their passwords against dictionary attacks! Find out how.

Definition • October 29, 2024
What is FGPP, or how to apply a refined password policy?
What is an FGPP, or fine-tuned password policy, in the context of Active Directory? How does it differ from GPOs? How do you apply it? We tell you all about it.

Word from the expert • October 29, 2024
Understand the concept of cybersecurity to (better) protect your business
Among all the sensitive subjects linked to the development of digital technology in the workplace, there is one that worries us more than any other: cybersecurity. Here's how it works.

Tip • November 16, 2020
Everything about Corporate Data Security Policy and Procedures
What is data security policy and why is it so important? Here are the main elements to include in a data security policy and other details.